Malware analysis Malicious activity
Por um escritor misterioso
Last updated 06 novembro 2024
A state-of-the-art survey of malware detection approaches using data mining techniques, Human-centric Computing and Information Sciences

A basic malware analysis method - ScienceDirect

Cybersecurity Search Engine

How to Do Malware Analysis?
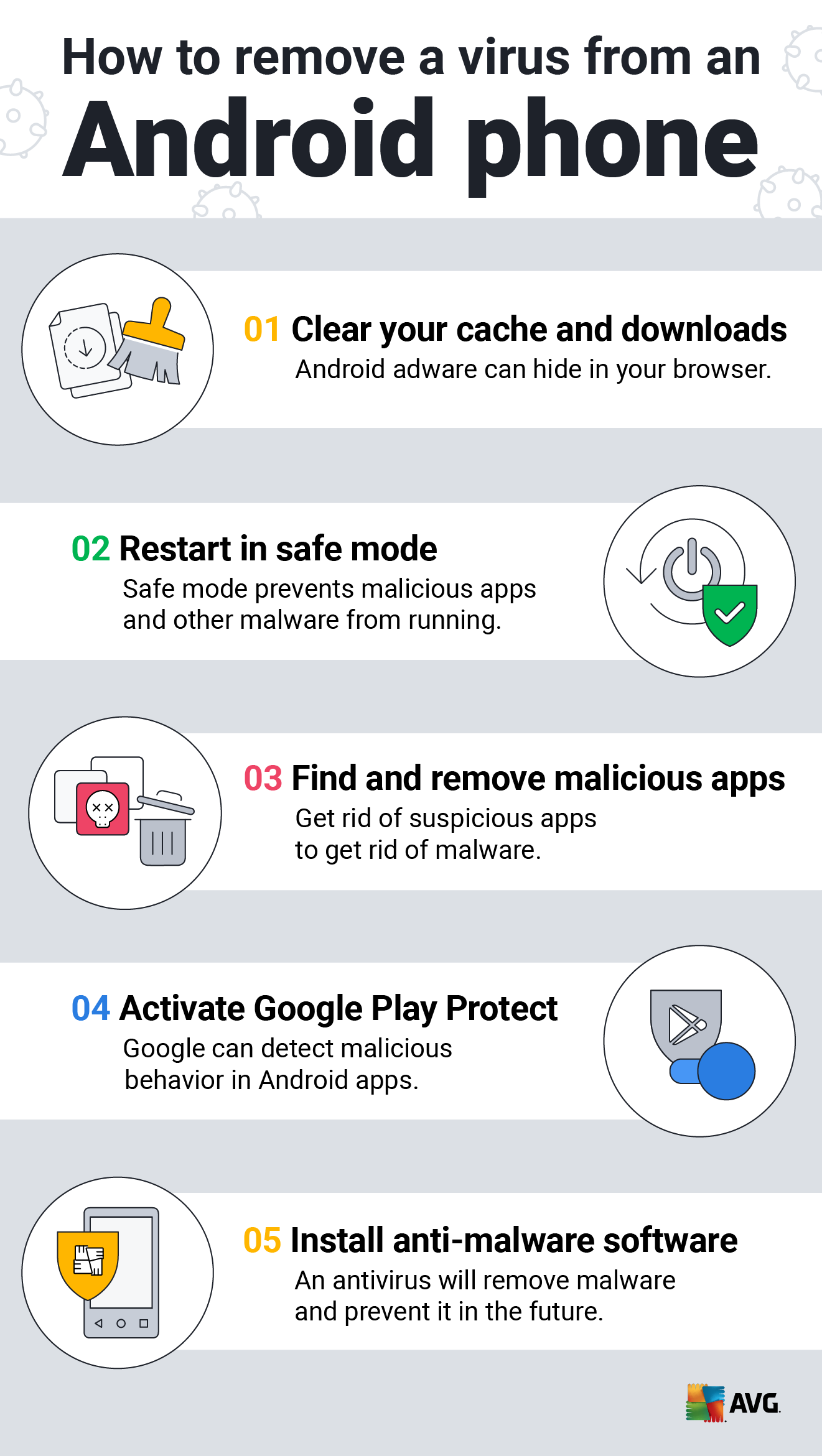
How to Clean an Android or iPhone from Viruses for Free
Symmetry, Free Full-Text
Lab 6-1 Solutions - Practical Malware Analysis [Book]

FBI, CISA, MS-ISAC release cybersecurity advisory on emerging Rhysida ransomware targeting critical sectors - Industrial Cyber

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen

UK and allies support Ukraine calling out Russia's GRU for
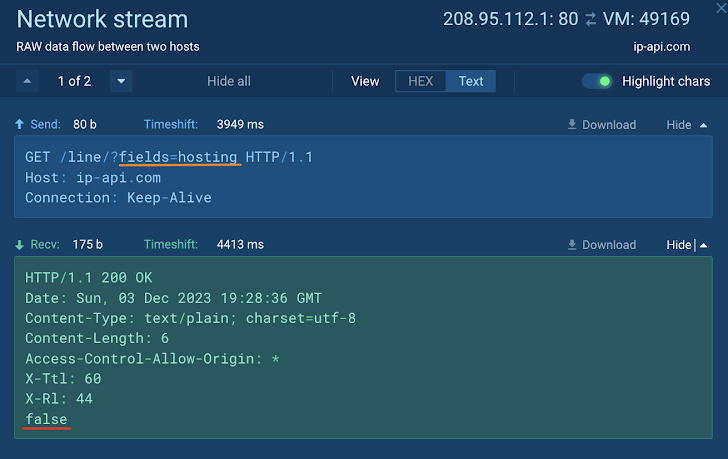
How to Analyze Malware's Network Traffic in A Sandbox

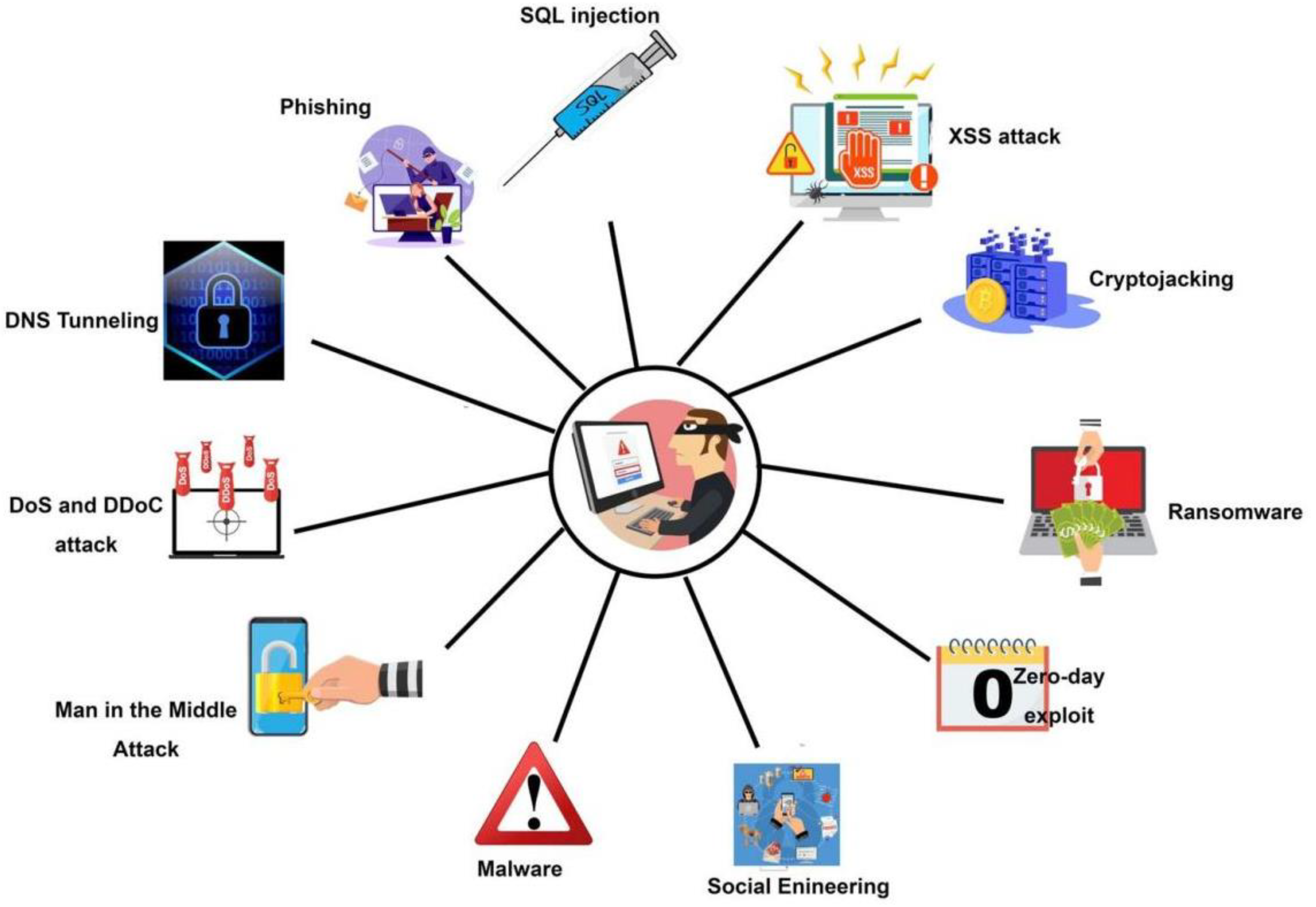
What is Malware? Definition, Types, Prevention - TechTarget

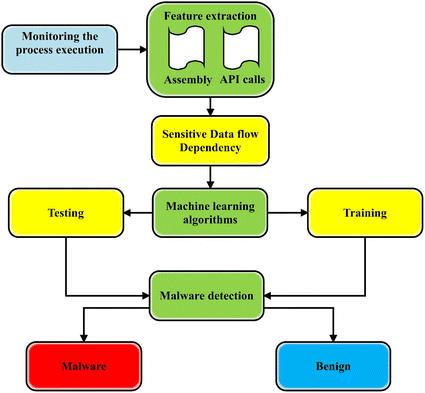
Process of traditional signature-based malware detection. [14]
Recomendado para você
-
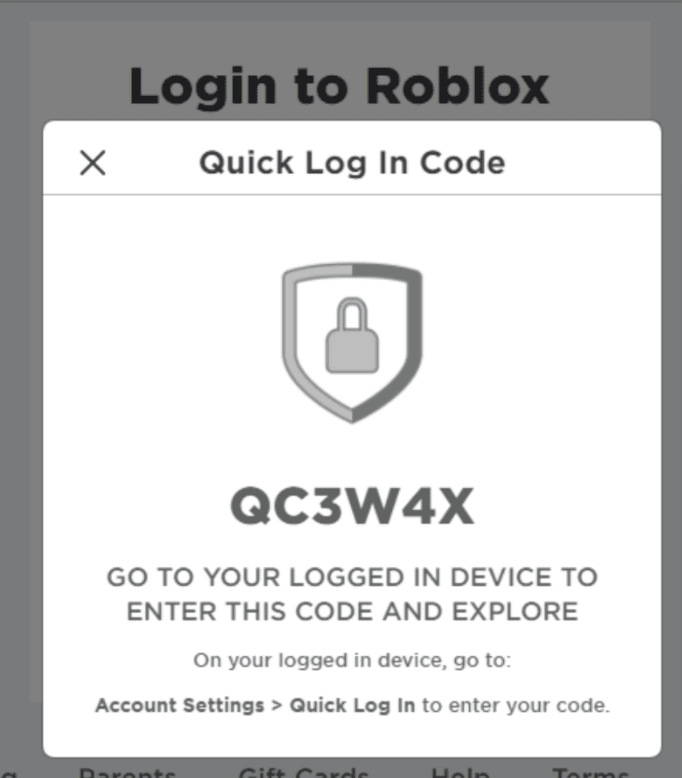 How To Use Roblox Quick Login: Easy Guide 2022 - BrightChamps Blog06 novembro 2024
How To Use Roblox Quick Login: Easy Guide 2022 - BrightChamps Blog06 novembro 2024 -
 Ysko on X: I like the new roblox login page / X06 novembro 2024
Ysko on X: I like the new roblox login page / X06 novembro 2024 -
 Roblox 2019 Login & Site06 novembro 2024
Roblox 2019 Login & Site06 novembro 2024 -
 Roblox false bans: How to get your account unbanned - Dexerto06 novembro 2024
Roblox false bans: How to get your account unbanned - Dexerto06 novembro 2024 -
 Testing sites, Roblox Wiki06 novembro 2024
Testing sites, Roblox Wiki06 novembro 2024 -
 Website of the Roblox Game MeepCity. Editorial Stock Photo - Image06 novembro 2024
Website of the Roblox Game MeepCity. Editorial Stock Photo - Image06 novembro 2024 -
 How To Drop Items in Roblox (2021)06 novembro 2024
How To Drop Items in Roblox (2021)06 novembro 2024 -
 Is a login screen allowed to be published? - Game Design Support06 novembro 2024
Is a login screen allowed to be published? - Game Design Support06 novembro 2024 -
 Roblox Website Stock Photos - Free & Royalty-Free Stock Photos06 novembro 2024
Roblox Website Stock Photos - Free & Royalty-Free Stock Photos06 novembro 2024 -
 Infinite Fun Captcha on Login page - Website Bugs - Developer06 novembro 2024
Infinite Fun Captcha on Login page - Website Bugs - Developer06 novembro 2024
você pode gostar
-
/cdn.vox-cdn.com/uploads/chorus_image/image/15735767/icewrestlingbros.0.jpg) Here are some bros wrestling on a frozen river in 191006 novembro 2024
Here are some bros wrestling on a frozen river in 191006 novembro 2024 -
Reagindo ao meu cancelamento, to de pijama #leoomk @donshai_shadow06 novembro 2024
-
 Mortal Kombat 1 PC Performance Analysis06 novembro 2024
Mortal Kombat 1 PC Performance Analysis06 novembro 2024 -
 Big Floppa - Caracal, Big Cat Meme - Funny, Modern, Subversive Cross Stitch Pattern - Digital PDF06 novembro 2024
Big Floppa - Caracal, Big Cat Meme - Funny, Modern, Subversive Cross Stitch Pattern - Digital PDF06 novembro 2024 -
 Tips to download from to Android06 novembro 2024
Tips to download from to Android06 novembro 2024 -
 Octopath Traveler: Champions of the Continent Pre-Registration Available Now for iOS and Android06 novembro 2024
Octopath Traveler: Champions of the Continent Pre-Registration Available Now for iOS and Android06 novembro 2024 -
 King Canute06 novembro 2024
King Canute06 novembro 2024 -
 The King of Fighters 2000 - SuperCombo Wiki06 novembro 2024
The King of Fighters 2000 - SuperCombo Wiki06 novembro 2024 -
 My Hero Academia Gets Original 2-Episode Anime This Summer - News - Anime News Network06 novembro 2024
My Hero Academia Gets Original 2-Episode Anime This Summer - News - Anime News Network06 novembro 2024 -
 Gaming Channel Name Ideas 202106 novembro 2024
Gaming Channel Name Ideas 202106 novembro 2024
