SQL injection and XSS: what white hat hackers know about trusting
Por um escritor misterioso
Last updated 15 junho 2024

Software developers have a lot on their minds. There are are myriad of questions to ask when it comes to creating a website or application: What technologies will we use? How will the architecture be set up? What functions do we need? What will the UI look like? Especially
Software developers have a lot on their minds. There are are myriad of questions to ask when it comes to creating a website or application: What technologies will we use? How will the architecture be set up? What functions do we need? What will the UI look like? Especially in a software market where shipping new apps seems more like a race for reputation than a well-considered process, one of the most important questions often falls to the bottom of the “Urgent” column: how will our product be
Software developers have a lot on their minds. There are are myriad of questions to ask when it comes to creating a website or application: What technologies will we use? How will the architecture be set up? What functions do we need? What will the UI look like? Especially in a software market where shipping new apps seems more like a race for reputation than a well-considered process, one of the most important questions often falls to the bottom of the “Urgent” column: how will our product be

Tool Release: Magisk Module – Conscrypt Trust User Certs, NCC Group Research Blog

Ethical hacking for IoT: Security issues, challenges, solutions and recommendations - ScienceDirect

SQL injection and cross-site scripting: The differences and attack anatomy
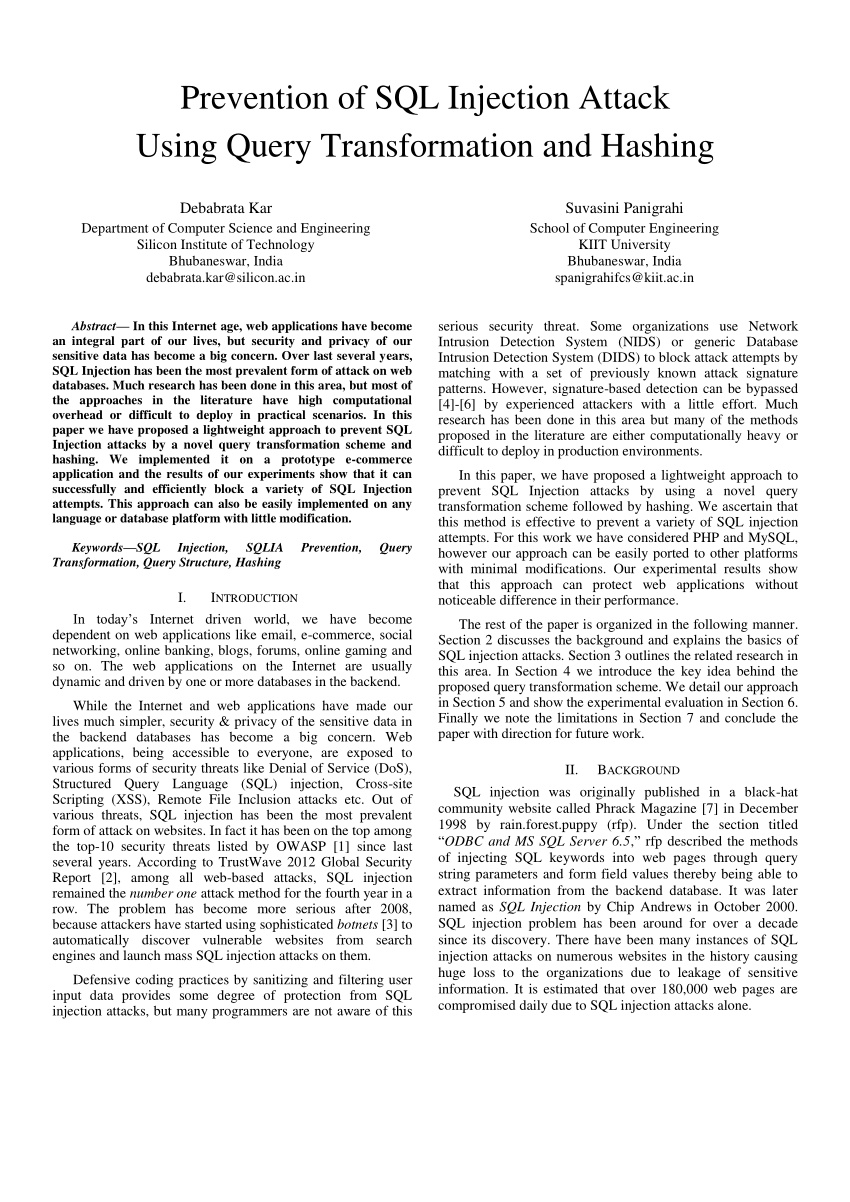
PDF) Prevention of SQL Injection attack using query transformation and hashing

Sql injections
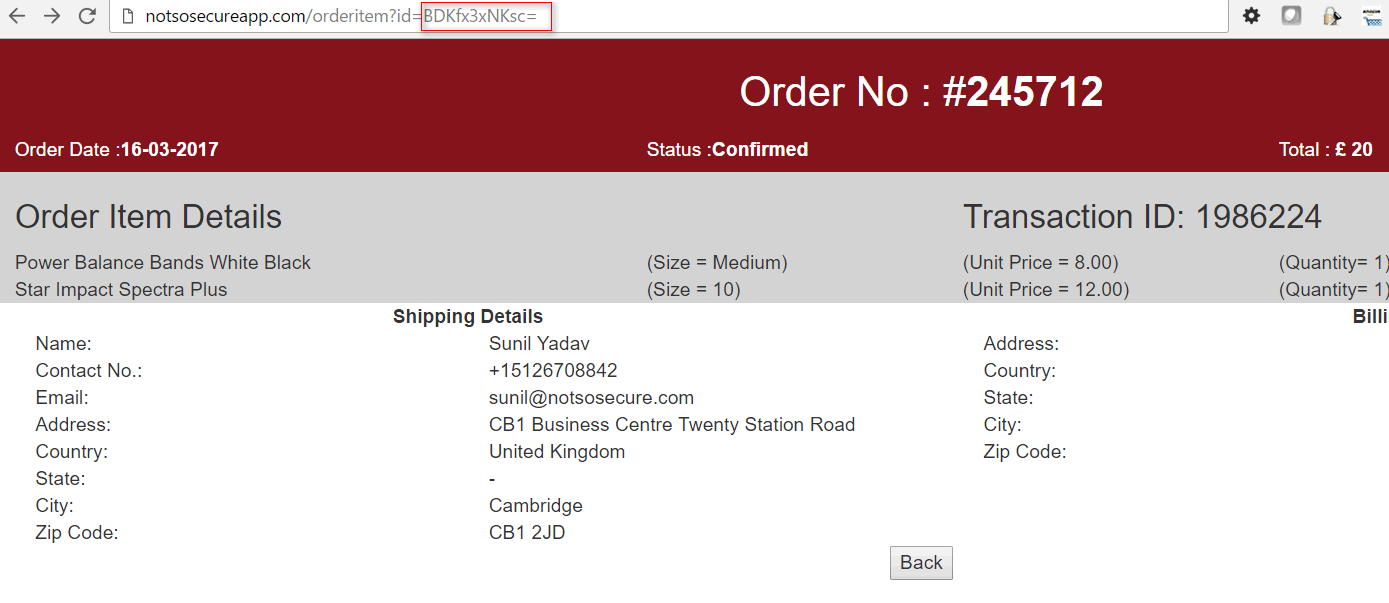
Anatomy of a Hack: SQLi via Crypto
Hackers are Googling your plain text passwords: preventing sensitive data exposure

What is Ethical Hacking? Know Ethical Hacking Skills, Career Path, Eligibility & Courses
Introduction to SQL Injection Attack, by Edward Low

Free Ethical Hacking Tutorial - Lee's Web Hacking (XSS , SQL Injection)

XSS (Cross-site scripting) Greeting Card for Sale by findingNull

40+ Best Cross-Site Scripting (XSS) Courses and Certifications for 2023

What Is Hacking? - White Hat, Black Hat, Gray Hat Hackers
Recomendado para você
-
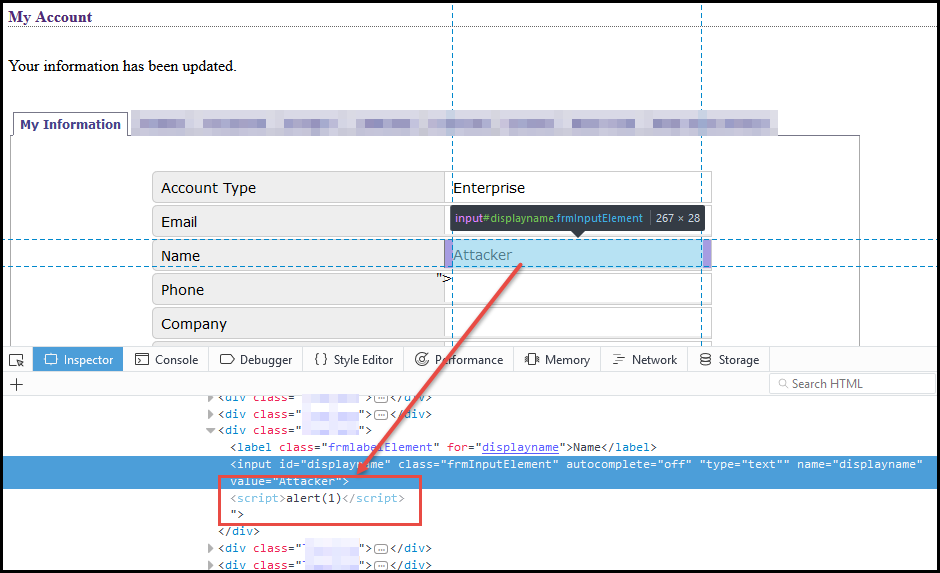 Weaponizing self-xss - NetSPI15 junho 2024
Weaponizing self-xss - NetSPI15 junho 2024 -
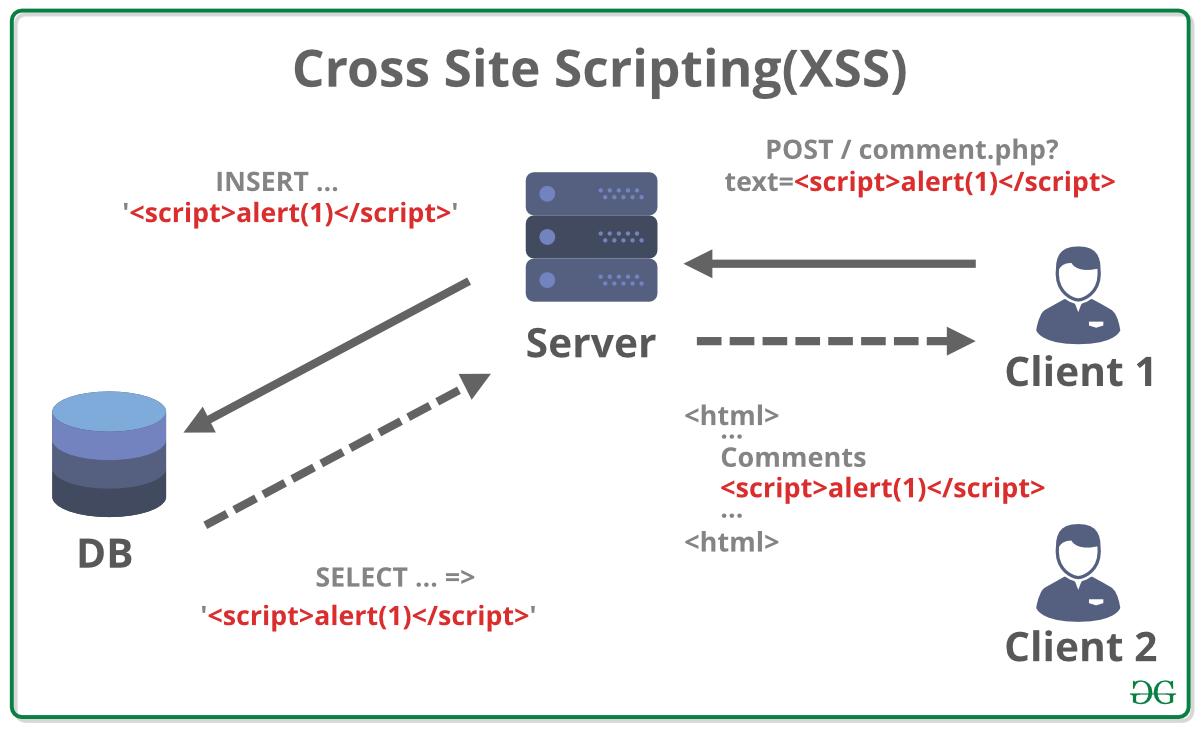 What is Cross Site Scripting (XSS) ? - GeeksforGeeks15 junho 2024
What is Cross Site Scripting (XSS) ? - GeeksforGeeks15 junho 2024 -
What is stored cross-site scripting? - Quora15 junho 2024
-
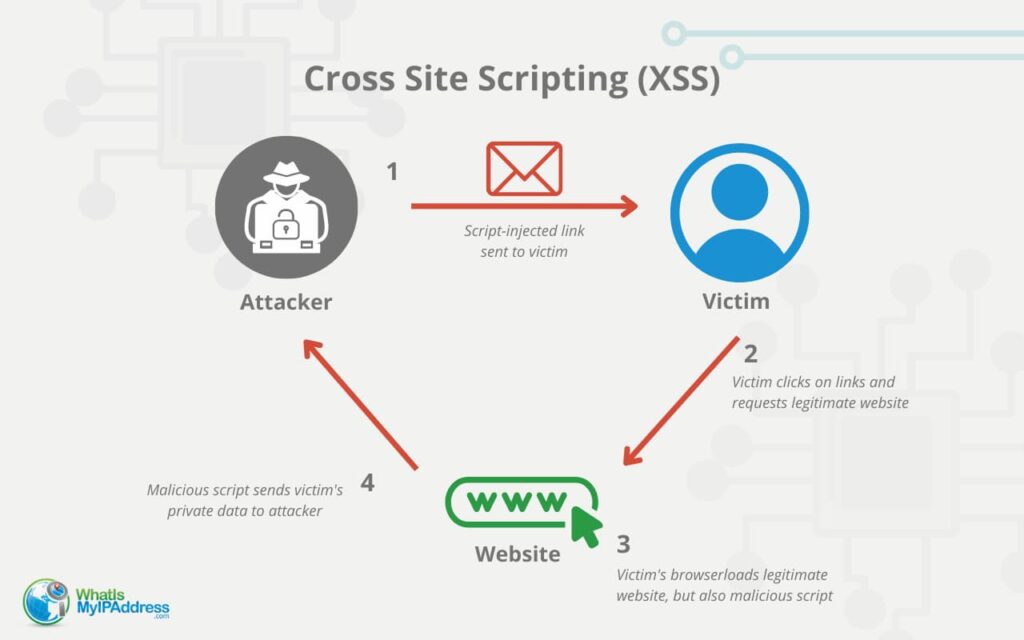 Cross-Site Scripting (XSS) Attacks Explained15 junho 2024
Cross-Site Scripting (XSS) Attacks Explained15 junho 2024 -
 Cross-Site Scripting (XSS) Attack in Modern Frontend Web15 junho 2024
Cross-Site Scripting (XSS) Attack in Modern Frontend Web15 junho 2024 -
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://d3i71xaburhd42.cloudfront.net/c976c25cbfcac95b7f9ca9b5783a731a75426605/1-Figure1-1.png) PDF] Figure 1: Architecture of XSS attack Injection of code into15 junho 2024
PDF] Figure 1: Architecture of XSS attack Injection of code into15 junho 2024 -
 Understanding Cross-Site Scripting Attacks15 junho 2024
Understanding Cross-Site Scripting Attacks15 junho 2024 -
 Difference Between XSS and SQL Injection15 junho 2024
Difference Between XSS and SQL Injection15 junho 2024 -
What are Injection attacks, and how to prevent them?15 junho 2024
-
 About cross-site scripting (XSS) attacks15 junho 2024
About cross-site scripting (XSS) attacks15 junho 2024
você pode gostar
-
 Top 10 requiem stands ideas and inspiration15 junho 2024
Top 10 requiem stands ideas and inspiration15 junho 2024 -
 Bruno's Onix, International Pokédex Wiki15 junho 2024
Bruno's Onix, International Pokédex Wiki15 junho 2024 -
 I made a Phil Spencer/PC GamePass meme for my latest clip15 junho 2024
I made a Phil Spencer/PC GamePass meme for my latest clip15 junho 2024 -
O segredo por trás do teste dos Aventureiros que garante sua confiança15 junho 2024
-
 Star Wars: The Last Jedi' Surprising Rotten Tomatoes Audience Score Revealed15 junho 2024
Star Wars: The Last Jedi' Surprising Rotten Tomatoes Audience Score Revealed15 junho 2024 -
 Five Nights at Freddy's: Security Breach Free Download » SteamRiP : r/SteamRip15 junho 2024
Five Nights at Freddy's: Security Breach Free Download » SteamRiP : r/SteamRip15 junho 2024 -
 Parents' Ultimate Guide to TikTok15 junho 2024
Parents' Ultimate Guide to TikTok15 junho 2024 -
 Best multiple Games in one App All Online Games available in15 junho 2024
Best multiple Games in one App All Online Games available in15 junho 2024 -
Code captain commando arcade APK (Android App) - Baixar Grátis15 junho 2024
-
Sub-Zero Mortal Kombat 1 4K Wallpaper iPhone HD Phone #6441k15 junho 2024

