Cybercriminals are circumventing email security with image-based
Por um escritor misterioso
Last updated 14 junho 2024
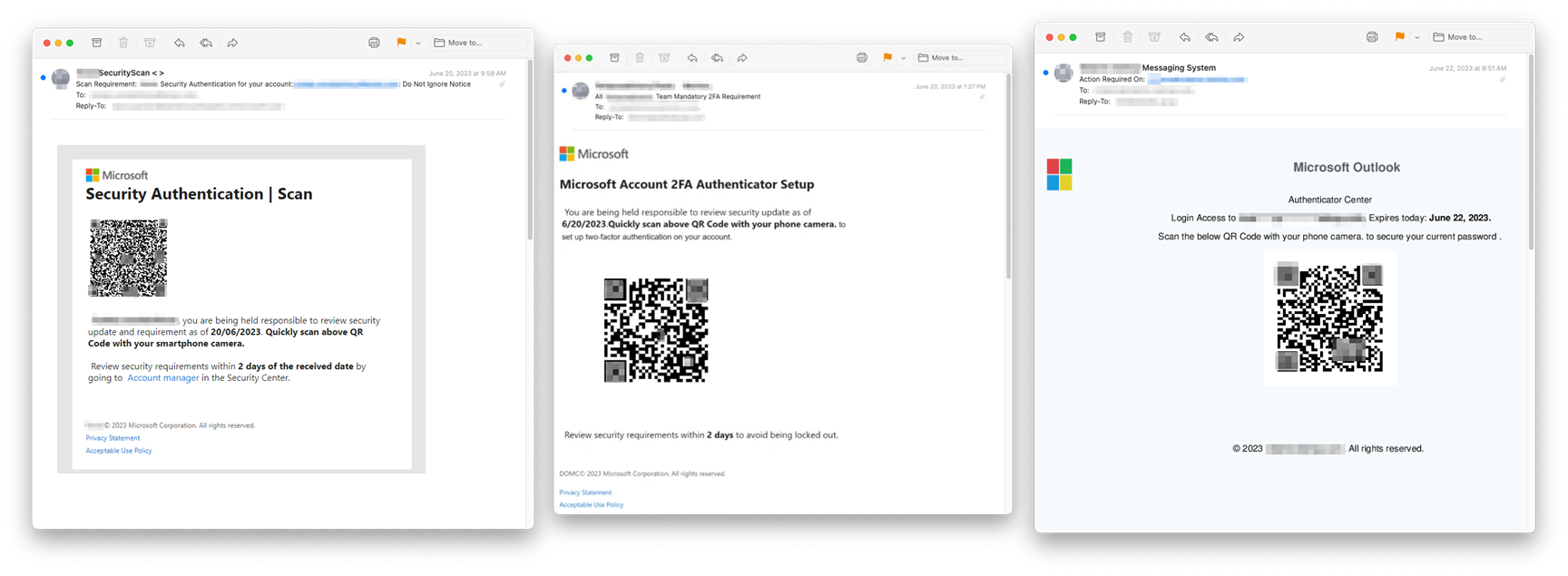
Security researchers at Inky recently discovered a rash of fraudulent emails that bypass certain conventional spam filters by using image attachments and QR codes. The scams don't
Security researchers at Inky recently discovered a rash of fraudulent emails that bypass certain conventional spam filters by using image attachments and QR codes. The scams don't
Security researchers at Inky recently discovered a rash of fraudulent emails that bypass certain conventional spam filters by using image attachments and QR codes. The scams don't

Four ways cyber-criminals fly under the radar

Hackers Are Bypassing Your Email Security Solution & Here's Ho - Guardian Digital .

Email Security Tech: No Guarantee of Protection from BEC - eftsure

What is Phishing Email: Examples, Types, Techniques & more

Staying One Step Ahead: Advanced Techniques for Email Security

Fileless attacks surge as cybercriminals evade cloud security defenses

4 best email security tools you need in your stack

Cybercriminals are circumventing email security with image-based scams

Cybercrime and AI : same threats now powered with advanced technology - Michalsons

20 Eye-Opening Cybercrime Statistics

Microsoft: BEC Attackers Evade 'Impossible Travel' Flags With Residential IP Addresses

Four ways cybercriminals can hack passwords

Thinking Strategically about Email Security in 2021 and Beyond - Guardian Digital .
What is Phishing Email: Examples, Types, Techniques & more
Recomendado para você
-
 Roblox Pls Donate Codes (June 2023) - Prima Games14 junho 2024
Roblox Pls Donate Codes (June 2023) - Prima Games14 junho 2024 -
 Roblox: Códigos de Evasão (outubro de 2023) - CenárioMT14 junho 2024
Roblox: Códigos de Evasão (outubro de 2023) - CenárioMT14 junho 2024 -
 Evade Roblox ID - Roblox music codes14 junho 2024
Evade Roblox ID - Roblox music codes14 junho 2024 -
 All Evade Codes in Roblox (December 2023)14 junho 2024
All Evade Codes in Roblox (December 2023)14 junho 2024 -
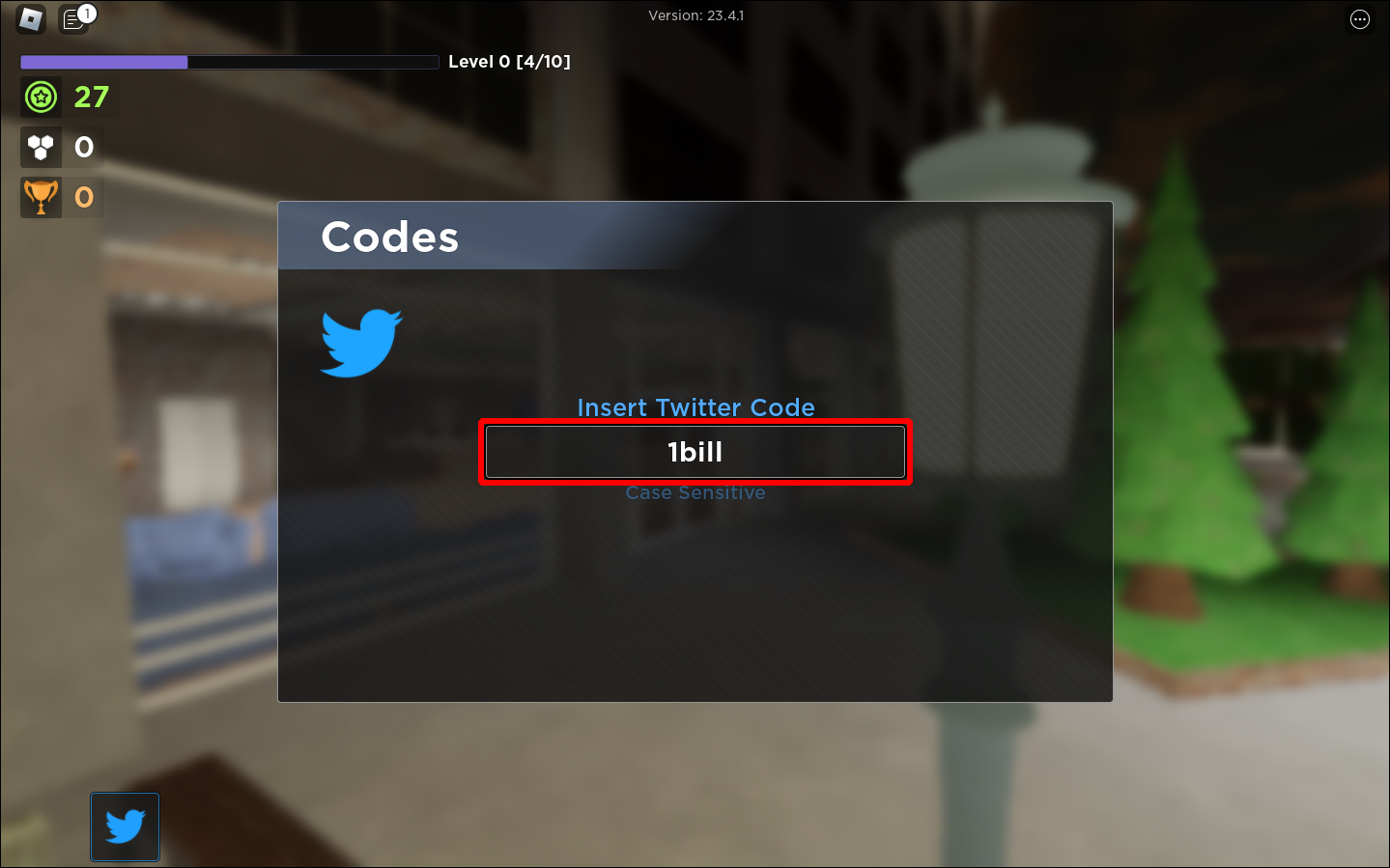 All Evade Codes(Roblox) - Tested December 2022 - Player Assist14 junho 2024
All Evade Codes(Roblox) - Tested December 2022 - Player Assist14 junho 2024 -
 Roblox Evolution Evade Codes (December 2023) - Pro Game Guides14 junho 2024
Roblox Evolution Evade Codes (December 2023) - Pro Game Guides14 junho 2024 -
 All Evade Codes For November 2023 - GameRiv14 junho 2024
All Evade Codes For November 2023 - GameRiv14 junho 2024 -
 Pro-Palestinian social media users turn to algospeak to avoid14 junho 2024
Pro-Palestinian social media users turn to algospeak to avoid14 junho 2024 -
 20% Off Evade PROMO CODE, COUPONS October 202314 junho 2024
20% Off Evade PROMO CODE, COUPONS October 202314 junho 2024 -
 Deena So'Oteh14 junho 2024
Deena So'Oteh14 junho 2024
você pode gostar
-
 Pin de ʜᴀʀᴜᴍɪ en ꜰᴜᴍᴇᴛꜱᴜ ɴᴏ ᴀɴᴀᴛᴀ ᴇ14 junho 2024
Pin de ʜᴀʀᴜᴍɪ en ꜰᴜᴍᴇᴛꜱᴜ ɴᴏ ᴀɴᴀᴛᴀ ᴇ14 junho 2024 -
 Pet Blobfish Meme Funny Blob Fish Blobfish Gifts T-shirt14 junho 2024
Pet Blobfish Meme Funny Blob Fish Blobfish Gifts T-shirt14 junho 2024 -
 Quiz História (4º Bimestre) - ProProfs Quiz14 junho 2024
Quiz História (4º Bimestre) - ProProfs Quiz14 junho 2024 -
 Kamisama ni Natta Hi Episode 1 pinterest, kami sama ni natta hi HD phone wallpaper14 junho 2024
Kamisama ni Natta Hi Episode 1 pinterest, kami sama ni natta hi HD phone wallpaper14 junho 2024 -
 My Stepmom's Daughter Is My Ex - Episódio 1 (Legendado) - BiliBili14 junho 2024
My Stepmom's Daughter Is My Ex - Episódio 1 (Legendado) - BiliBili14 junho 2024 -
 Phil Spencer: The Number of PC Game Pass Users Has Quadrupled in Japan14 junho 2024
Phil Spencer: The Number of PC Game Pass Users Has Quadrupled in Japan14 junho 2024 -
 Super Saiyajin 5, Wiki14 junho 2024
Super Saiyajin 5, Wiki14 junho 2024 -
 Gashapon JoJo's Bizarre Adventure Stand Figure Collection 01 Set : Toys & Games14 junho 2024
Gashapon JoJo's Bizarre Adventure Stand Figure Collection 01 Set : Toys & Games14 junho 2024 -
 First The Lord Of The Rings Gollum Screens Released - My Precious! - PlayStation Universe14 junho 2024
First The Lord Of The Rings Gollum Screens Released - My Precious! - PlayStation Universe14 junho 2024 -
 Ralph Lauren UES & Ralph's Coffee // Christmas in NYC14 junho 2024
Ralph Lauren UES & Ralph's Coffee // Christmas in NYC14 junho 2024